Adaptive Remainder Modulo m Data Hiding
Keywords:
Adaptation, data hiding, ensemble of classifiers, remainder modulo, RS-diagram, SPAM featuresAbstract
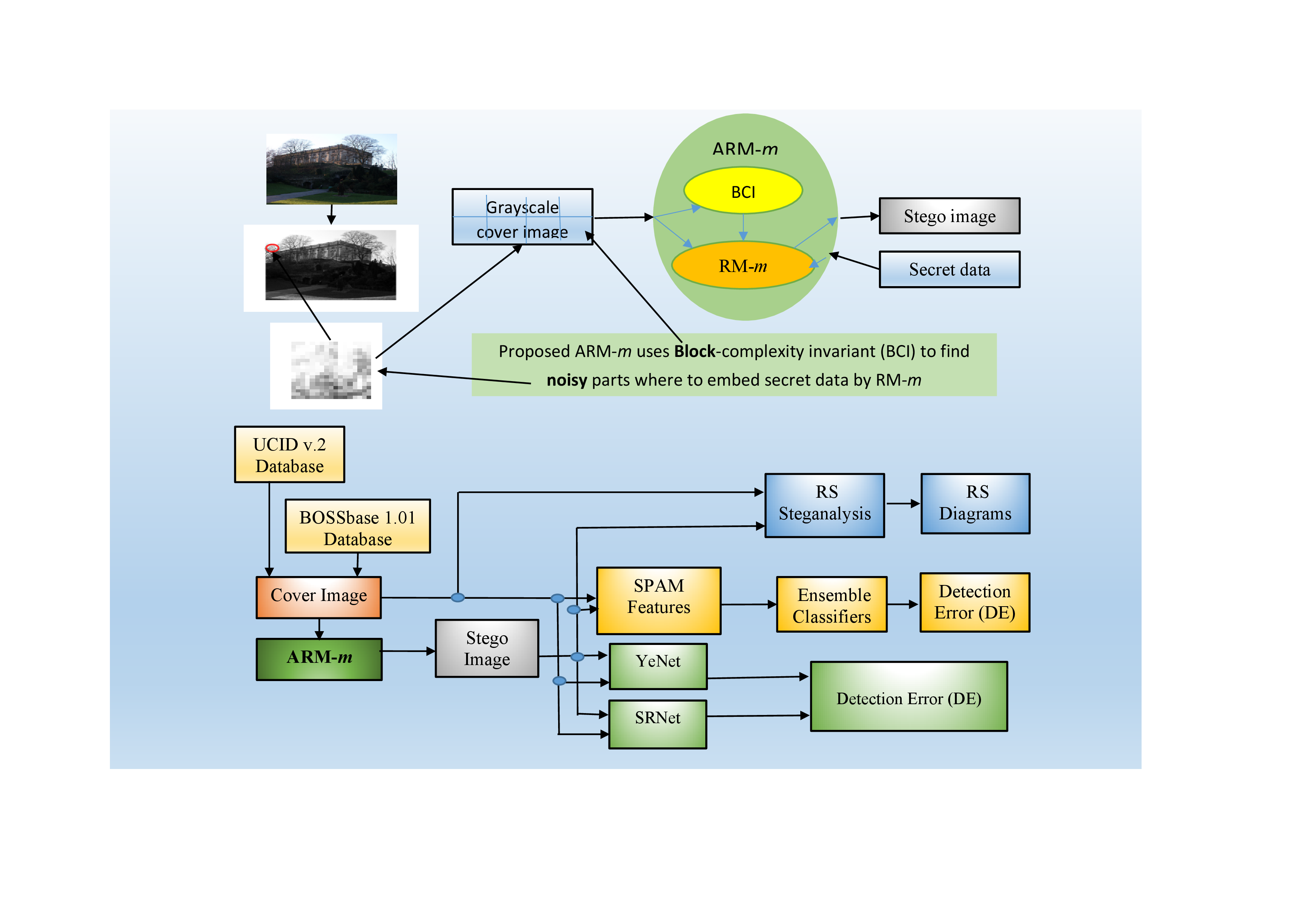
A problem of irreversible data hiding (DH), producing stego images resistant to steganalysis, is considered in spatial domain of gray-scale cover images. Stego image detection error (DE) is maximized when data is hidden (embedded) into noisy-like image areas where pixel values vary significantly. It is proved herein that generalization of the well-known least-significant bit (LSB) substitution to remainder modulo m (RM-m) DH method has an embedding invariant preserved after DH. A new adaptive remainder modulo m (ARM-m) method hiding data first in maximal noisy blocks by RM-m is proposed. ARM-m uses the invariant to construct a block complexity measure for adaptation. Ensemble classifiers and subtractive pixel adjacency matrix (SPAM) with 686 features were used to evaluate stego image DE on 886 images from UCID v.2 database. Compared to the state-of-the-art methods, ARM-4 with 2x2 blocks has DE=41.86% versus 24.42% of the best known method for 1 bit per pixel (bpp) embedding rate (ER). For ER=1.33 bpp, not reachable for known adaptive methods, ARM-4 and ARM-16, both with 8x8 blocks, have DE=27.33% and 27.91%, respectively. ARM-4 is confirmed to be better than other methods also for 2658 gray scale images. RS-diagram steganalysis conducted complies with DE evaluation results.
Downloads
References
R. Bohme, Advanced Statistical Steganalysis, vol. 16, Springer, 2010, pp. 288. doi: https://doi.org/10.1007/978-3-642-14313-7.
I. J. Kadhim , P. Premaratne, P. J. Vial and B. Halloran, "Comprehensive survey of image steganography: Techniques, Evaluations, and trends in future research," Neurocomputing, vol. 335, p. 299–326, 2019. doi: https://doi.org/ 10.1016/j.neucom.2018.06.075.
T. Filler, J. Judas and J. Fridrich, "Minimizing additive distortion in steganography using syndrome-trellis codes," IEEE Transactions on Information Forensics and Security, vol. 6, no. 3, pp. 920-935, September 2011. doi: 10.1109/TIFS.2011.2134094.
E. Ansari, M. Keshtkaran, R. Wallace, S. M. Mirsadegh and F. Ansari, "OOPAP and OPVD: Two innovative improvements for hiding secret data into images," Iran J Sci Technol Trans Electr Eng, vol. 43, pp. 55-65, 2019. doi: https://doi.org/10.1007/s40998-018-0090-4.
A. Chefranov and G. Öz, "On LSB, LSB OPAP, and LSB OOPAP published experimental results correctness," Iranian Journal of Science and Technology, Transactions of Electrical Engineering, vol. 46, p. 609–619, June 2022. doi: https://doi.org/ 10.1007/s40998-022-00491-8.
E. Kawaguchi, "BPCS-steganography - principle and applications," in 9th International Conference, KES 2005, Proceedings, Part IV, Melbourne, Australia, September 14-16, 2005, 2005.
M. Khodaei, B. Bigham and K. Faez, "Adaptive data hiding, using pixel-value differencing and LSB substitution," Cybernetics and Systems, vol. 47, no. 8, pp. 617-628, 2016. doi: 10.1080/01969722.2016.1214459.
T. D. Nguyen, S. Arch-int and N. Arch-int, "An adaptive multi bit-plane image steganography using block data-hiding," Multimed Tools Appl, vol. 75, p. 8319–8345, 2016. doi: 10.1007/s11042-015-2752-9.
B. C. Nguyen, S. M. Yoon and H.-K. Lee, "Multi bit plane image steganography," in Digital Watermarking. IWDW 2006, 4283, pp. 61-70, Berlin Heidelberg, 2006. doi: https://doi.org/ 10.1007/11922841_6.
S.-J. Wang, "Steganography of capacity required using modulo operator for embedding secret image," Applied Mathematics and Computation, vol. 164, pp. 99-116, 2005. doi: https://doi.org/10.1016/j.amc.2004.04.059.
T. Pevný, P. Bas and J. Fridrich, "Steganalysis by subtractive pixel adjacency matrix," IEEE Transactions on Information Forensics and Security, vol. 5, no. 2, pp. 215-224, June 2010. doi: 10.1109/TIFS.2010.2045842.
C.-K. Chan and L. M. Cheng, "Hiding data in images by simple LSB substitution," Pattern Recognition, vol. 37, p. 469 – 474, 2004. doi: https://doi.org/ 10.1016/j.patcog.2003.08.007.
K. A. Darabkh, A. K. Al-Dhamar and I. F. Jafar, "A new steganographic algorithm based on Multi Directional PVD and Modified LSB," Information Tevhnology and Control, vol. 46, no. 1, pp. 16-36, 2017. doi: 10.5755/j01.itc.46.1.15253.
V. Sabeti, S. Samavi and S. Shirani, "An adaptive LSB matching steganography based on octonary complexity measure," Multimed. Tools Appl., vol. 64, p. 777–793, 2013. doi: 10.1007/s11042-011-0975-y.
J. Bai, C.-C. Chang, T.-S. Nguyen, C. Zhu and Y. Liu, "A high payload steganographic algorithm based on edge detection," Displays, vol. 46, pp. 42-51, 2017. doi: http://dx.doi.org/10.1016/j.displa.2016.12.004.
M. R. Islam, T. R. Tanni, S. Parvin and M. J. Sultan, "A modified LSB image steganography method using filtering algorithm and stream of password," Information Security Journal: A Global Perspective, pp. 1-12, November 2020. doi: https://doi.org/ 10.1080/19393555.2020.1854902.
M. Hussain, Q. Riaz, S. Saleem, A. Ghafoor and K.-H. Jung, "Enhanced adaptive data hiding method using LSB and pixel value differencing," Multimedia Tools and Applications, vol. 80, p. 20381–20401, 2021. doi: https://doi.org/ 10.1007/s11042-021-10652-2.
W. Wu and H. Li, "A novel scheme for random sequential high-capacity data hiding based on PVD and LSB," Signal, Image and Video Processing, vol. 10, p. 2277–2287, 2024. doi: https://doi.org/ 10.1007/s11760-023-02900-9.
C. H. Yang, C. Y. Weng, S. J. Wang and H.-M. Sun, "Adaptive data hiding in edge areas of images with spatial LSB domain systems.," IEEE Transactions Information Forensics and Security, vol. 3, no. 3, p. 488–497, 2008. doi: 10.1109/tifs.2008.926097.
M. Hussain, A. W. A. Wahab, A. Hoc, N. Javed and K.-H. Jung, "A data hiding scheme using parity-bit pixel value differencing and improved rightmost digit replacement," Signal Processing: Image Communication, vol. 50, p. 44–57, 2017. doi: https://doi.org/ 10.1016/j.image.2016.10.005.
H.-C. Wu, N.-I. Wu, C.-S. Tsai and M.-S. Hwang, "Image steganographic scheme based on pixel-value differencing and LSB replacement methods," IEE Proc.-Vis. Image Signal Process., vol. 152, no. 5, pp. 611-615, October 2005. doi: 10.1049/ip-vis:20059022.
C.-H. Yang, C.-Y. Weng, S.-J. Wang and H.-M. Sun, "Varied PVD+ LSB evading detection programs to spatial domain in data embedding systems," The Journal of Systems and Software, vol. 83, p. 1635–1643, 2010. doi: https://doi.org/10.1016/j.jss.2010.03.081.
D.-C. Wu and W.-H. Tsai, "A steganographic method for images by pixel-value differencing," Pattern Recognition Letters, vol. 24, p. 1613–1626, 2003. doi:10.1016/S0167-8655(02)00402-6.
D.-C. Wu and D. Chun, "Image Steganography by Pixel-Value Differencing Using General Quantization Ranges," Computer Modeling in Engineering & Sciences, vol. 141, no. 1, pp. 353-383, 2024. doi: https://doi.org/10.32604/cmes.2024.050813.
K.-C. Chang, C.-P. Chang, P. S. Huang and T.-M. Tu, "A novel image steganographic method using tri-way pixel-value differencing," Journal of Multimedia, vol. 3, no. 2, pp. 37-44, June 2008. doi:10.4304/jmm.3.2.37-44.
W. Luo and F. Huang, "Edge adaptive image steganography based on LSB matching revisited," IEEE Transactions on Information Forensics and Security, vol. 5, no. 2, pp. 201-214, June 2010. doi: 10.1109/TIFS.2010.2041812.
H.-H. Liu, P.-C. Su and M.-H. Hsu, "An improved steganography method based on least-significant-bit substitution and pixel-value differencing," KSII Transactions on Internet and Information Systems, vol. 14, no. 11, pp. 4537-4556, Nov. 2020. doi: http://doi.org/10.3837/tiis.2020.11.016.
M. Khodaei and K. Faez, "New adaptive steganographic method using least-significant-substitution and pixel-value differencing," IET Image Processing, pp. 1-10, August 2012. doi: 10.1049/iet-ipr.2011.0059.
S. Singh, "Adaptive PVD and LSB based high capacity data hiding scheme," Multimedia Tools and Applications, vol. 79, p. 18815–18837, 2020. doi: https://doi.org/ 10.1007/s11042-020-08745-5.
S. Kang, H. Park and J. Park, "Combining LSB embedding with modified Octa-PVD embedding," Multimedia Tools and Applications, vol. 79, pp. 21155-21175, August 2020. doi: https://doi.org/ 10.1007/s11042-020-08925-3.
G. Swain, "Digital image steganography using eight-directional PVD against RS analysis and PDH analysis," Advances in Multimedia, vol. 2018, no. 4847098, p. 13, 2018. doi: 10.1155/2018/4847098.
S. Swain, "Two new steganography techniques based on quotinet value differencing with addition-subtraction logic and PVD with modulus function,," Optik, vol. 180, pp. 807-823, February 2019. doi: https://doi.org/10.1016/j.ijleo.2018.11.015.
R. Sonar and G. Swain, "Steganography based on quotient value differencing and pixel value correlation," CAAI Transactions on Intelligence Technology, vol. 6, no. 4, pp. 504-519, December 2021. doi: https://doi.org/10.1049/cit2.12050.
S. Kosuru, A. Pradhan, K. A. Basith, R. Sonar and G. Swain, "Digital image steganography with error correction on xxtracted data," IEEE Access, vol. 11, pp. 80945-80957, 2023. doi: 10.1109/ACCESS.2023.3300918.
G. Swain, "Very high capacity image steganography technique using quotient value differencing and LSB substitution," Arabian Journal for Science and Engineering, vol. 44, p. 2995–3004, 2019. doi: https://doi.org/ 10.1007/s13369-018-3372-2.
D. B. Khadse and G. Swain, "Data hiding and integrity verification based on quotient value differencing and Merkle tree," Arabian Journal for Science and Engineering, vol. 48, p. 1793–1805, 2023. doi: https://doi.org/ 10.1007/s13369-022-06961-9.
A. Sur, V. Ramanathan and J. Mukherjee, "Pixel rearrangement based statistical restoration scheme reducing embedding noise," Multimed. Tools Appl., vol. 68, p. 805–825, 2014. doi: 10.1007/s11042-012-1078-0.
S. Sun, "A new information hiding method based on improved BPCS steganography," Advances in Multimedia, vol. 2015, p. 698492, 2015. doi: http://dx.doi.org/10.1155/2015/698492.
J. Fridrich, V. Holub and T. Denemark, July 2021. [Online]. Available: http://dde.binghamton.edu/download/feature_extractors/.
T. Filler, J. Fridrich and J. Judas, July 2021. [Online]. Available: http://dde.binghamton.edu/download/syndrome/.
Dataset, "Dataset of standard 512X512 grayscale test images," 2018. [Online]. Available: http://decsai.ugr.es/cvg/CG/base.htm. [Accessed 21 May 2025].
G. Schaefer and M. Stich, "UCID: an uncompressed color image database," in Storage and Retrieval Methods and Applications for Multimedia 2004, 20 January 2004, 5307, 472–481, San Jose, CA, USA, 2004. doi: https://doi.org/ 10.1117/12.525375.
J. Fridrich, M. Goljan and R. Du, "Detecting LSB steganography in color and gray-scale images," IEEE Multimedia, vol. 8, no. 4, pp. 22-28, October-December 2001. doi: 10.1109/93.959097.