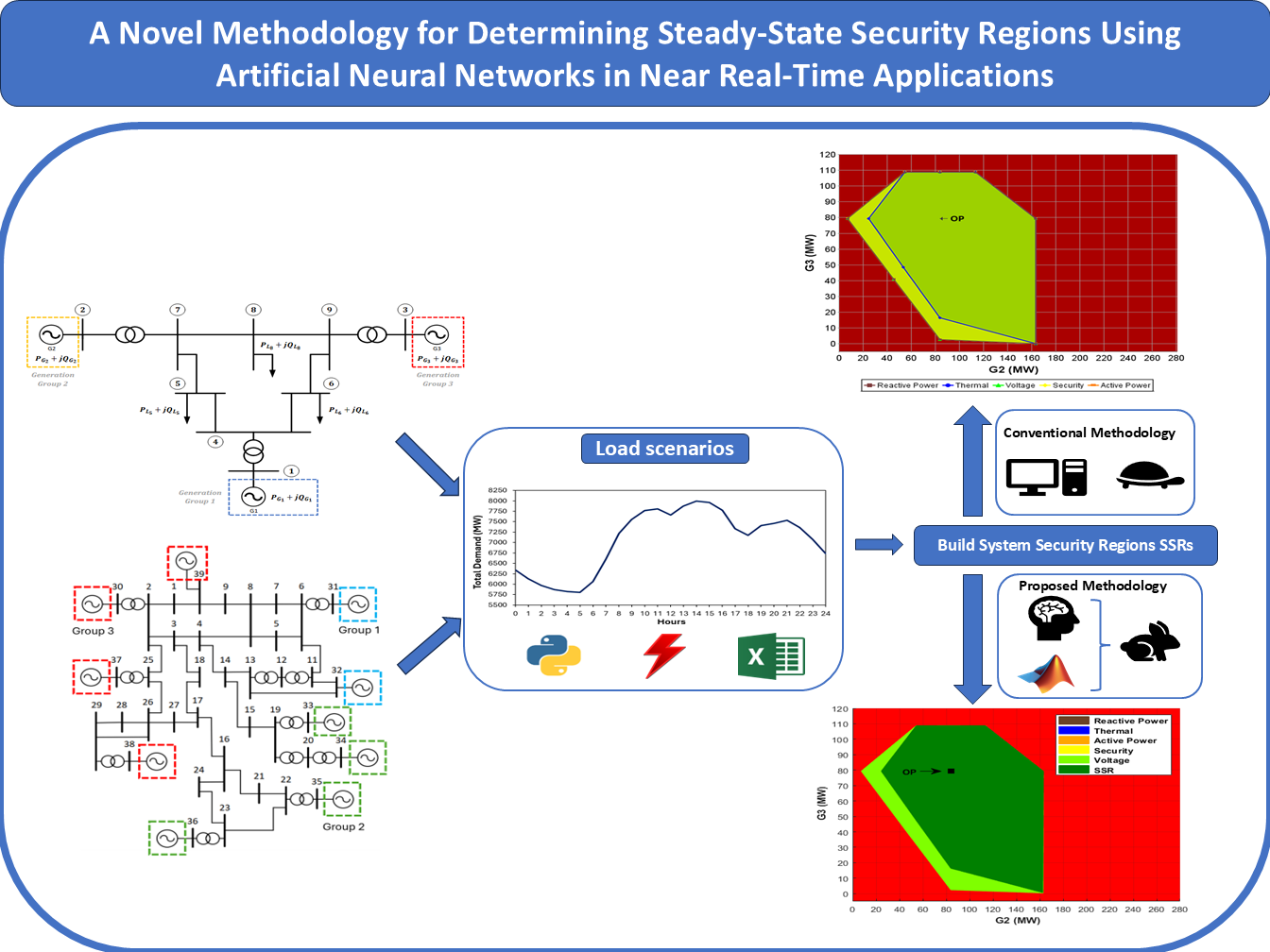
A Novel Methodology for Determining Steady-State Security Regions Using Artificial Neural Networks in Near Real-Time Applications
Keywords:
Artificial neural networks, power system operation, security assessment, steady-state security regionsAbstract
The increasing penetration of variable renewable energy sources, such as photovoltaic and wind power, poses significant challenges to the real-time security assessment of power systems. In this context, the Steady-State Security Regions framework has emerged as a robust tool for voltage security assessment, providing valuable insights into the steady-state operating limits of electrical networks. However, the computational burden associated with determining these regions during system operation remains a major obstacle for current methodologies. This paper presents a novel approach for efficiently identifying these regions using artificial neural networks, enabling the fast and accurate delineation of security boundaries suitable for real-time and near-real-time applications. The methodology was validated on the IEEE 9-Bus and New England test systems, achieving accuracy comparable to conventional techniques while reducing computational time by up to 96%. The results underscore the potential of the proposed method as a scalable and effective tool to support operational decision-making in power systems with high shares of renewable generation.
Downloads
References
T. Adefarati and R. Bansal, “Integration of renewable distributed generators into the distribution system: a review,” IET Renewable Power Generation, vol. 10, no. 7, pp. 873–884, 2016. doi: https://doi.org/10.1049/ietrpg.2015.0378 .
K. Morison, L. Wang, and P. Kundur, “Power system security assessment,” IEEE Power and Energy Magazine, vol. 2, no. 5, pp. 30–39, 2004. doi: 10.1109/MPAE.2004.1338120 .
K. Morison, “On-line dynamic security assessment using intelligent systems,” in 2006 IEEE Power Engineering Society General Meeting, 2006, pp. 5 pp.–. doi: 10.1109/PES.2006.1709501 .
F. C. Almeida, J. A. P. Filho, J. L. Pereira, R. M. Henriques, and A. L. Marcato, “Assessment of load modeling in power system security analysis based on static security regions,” Journal of Control, Automation and Electrical Systems, vol. 24, pp. 148–161, 4 2013. doi: 10.1007/s40313-013-0020-7 .
R. Diao, V. Vittal, and N. Logic, “Design of a real-time security assessment tool for situational awareness enhancement in modern power systems,” IEEE Transactions on Power Systems, vol. 25, no. 2, pp. 957–965, 2010. doi: 10.1109/TPWRS.2009.2035507 .
S. C. Savulescu, Real-time stability assessment in modern power system control centers. USA: John Wiley & Sons, 2009.
C. A. S. Neto, M. A. Quadros, M. G. Santos, and J. Jardim, “Brazilian system operator online security assessment system,” in IEEE PES General Meeting, 2010, pp. 1–7. doi: 10.1109/PES.2010.5590039 .
O. F. Avila, J. A. Passos Filho, and W. Peres, “Steady-state security assessment in distribution systems with high penetration of distributed energy resources,” Electric Power Systems Research, vol. 201, p.
, 2021. doi: https://doi.org/10.1016/j.epsr.2021.107500 .
J. Xiao, S. Zhang, Z. Qiu, C. Song, H. Jiao, and B. She, “Geometric property of distribution system security region: Size and shape,” Electric Power Systems Research, vol. 210, p. 108106, 2022. doi:
1016/j.epsr.2022.108106 .
J. Zhu, R. Fan, G. Xu, and C. Chang, “Construction of maximal steadystate security regions of power systems using optimization method,” Electric Power Systems Research, vol. 44, no. 2, pp. 101–105, 1998.
doi: 10.1016/S0378-7796(97)01188-7 .
R. A. G. Tinoco, J. A. Passos Filho, W. Peres, and R. M. Henriques, “A new particle swarm optimization-based methodology for determining online static security regions,” International Transactions on Electrical Energy Systems, vol. 31, no. 3, p. e12790, 2021. doi: https://doi.org/10.1002/2050-7038.12790 .
C.-C. Liu, “A new method for the construction of maximal steadystate security regions of power systems,” IEEE Transactions on Power Systems, vol. 1, no. 4, pp. 19–26, 1986. doi: 10.1109/TPWRS.
4335009 .
S. J. Chen, Q. X. Chen, Q. Xia, and C. Q. Kang, “Steady-state security assessment method based on distance to security region boundaries,” IET Generation, Transmission & Distribution, vol. 7, no. 3, pp. 288–297, 2013. doi: 10.1049/iet-gtd.2012.0288 .
F. Wu and S. Kumagai, “Steady-state security regions of power systems,” IEEE Transactions on Circuits and Systems, vol. 29, no. 11, pp. 703–711, 1982. doi: 10.1109/TCS.1982.1085091 .
F. Wu, Y.-K. Tsai, and Y.-X. Yu, “Probabilistic steady-state and dynamic security assessment,” IEEE Transactions on Power Systems, vol. 3, no. 1, pp. 1–9, 1988. doi: 10.1109/59.43173 .
H. Sarmiento, G. Pampin, R. Barajas, R. Castellanos, G. Villa, and M. Mirabal, “Nomograms for assistance in voltage security visualization,” in 2009 IEEE/PES Power Systems Conference and Exposition,
, pp. 1–6. doi: 10.1109/PSCE.2009.4840049 .
F. M. Tavela, J. A. Filho, and O. F. Avila, “Assessment of the impact of wind generation intermittency on electric power systems through security regions,” Journal of Control, Automation and Electrical Systems, vol. 33, pp. 982–997, 6 2022. doi: 10.1007/S40313-021-00870-2 .
H. Sun, D. Yu, and Y. Xie, “Flexible steady-state security region of power system with uncertain load demand and soft security limits,” in 2000 Power Engineering Society Summer Meeting
(Cat. No.00CH37134), vol. 4, 2000, pp. 2008–2013 vol. 4. doi:10.1109/PESS.2000.866955 .
S. Maihemuti, W. Wang, J. Wu, H. Wang, M. Muhedaner, and Q. Zhu, “New energy power system dynamic security and stability region calculation based on avurpso-rls hybrid algorithm,” Processes, vol. 11, no. 4, 2023. doi: 10.3390/pr11041269 .
Y. Yu, “Security region of bulk power system,” in Proceedings. International Conference on Power System Technology, vol. 1, 2002, pp. 13–17 vol.1. doi: 10.1109/ICPST.2002.1053495 .
J. D. McCalley, G. Zhou, and V. V. Acker, “Power system security boundary visualization using neural networks,” Neurocomputing, vol. 23, no. 1, pp. 85–96, 1998. doi: https://doi.org/10.1016/S0925-
(98)00077-0 .
J. Jardim, “Online dynamic security assessment: implementation problems and potential use of artificial intelligence,” in Power Engineering Society Summer Meeting, vol. 1, 2000, pp. 340–345. doi:
1109/PESS.2000.867607 .
M. Cuevas, R. A´ lvarez Malebra´n, C. Rahmann, D. Ortiz, J. Pen˜a, and R. Rozas-Valderrama, “Artificial intelligence techniques for dynamic security assessments - a survey,” Artificial Intelligence Review 2024
:12, vol. 57, pp. 1–43, 10 2024. doi: 10.1007/S10462-024-10993-Y .
D. Sun and Y. Yu, “Accurate identification of critical boundary hyperplanes of practical steady-state security region in distribution grids,” IEEE Transactions on Smart Grid, vol. 14, no. 6, pp. 4312–4321, 2023.
doi=10.1109/TSG.2023.3262693. doi: 10.1109/TSG.2023.3262693 .
S. Zhang, W. Gu, X.-P. Zhang, H. Lu, S. Lu, S. Ding, J. Wang, and S. Zhao, “Steady-state security region of integrated energy system considering thermal dynamics,” IEEE Transactions on Power
Systems, vol. 39, no. 2, pp. 4138–4153, 2024. doi: 10.1109/TPWRS.2023.3296080 .
P. M. Anderson and A. A. Fouad, Power system control and stability. John Wiley & Sons, 2008.
G. Bills, “On-line stability analysis study, rp 90-1,” North American Rockwell Information Systems Co., Anaheim, CA (USA), Tech. Rep., 1970.
F. C. B. Almeida, J. A. P. Filho, J. L. R. Pereira, A. L. M. Marcato, and E. J. de Oliveira, “Assessment of the generator remote voltage control through static security regions,” in 2011 IEEE Power and Energy Society General Meeting, 2011, pp. 1–7. doi: 10.1109/PES.2011.6039630 .
J. Heaton, Introduction to Neural Networks with Java. Saint Louis: Heaton Research, 2008.
N. Friedman and D. Koller, “Being bayesian about network structure. a bayesian approach to structure discovery in bayesian networks,” Machine learning, vol. 50, pp. 95–125, 2003. doi: 10.1023/A:1020249912095 .
M. H. Beale, M. T. Hagan, and H. B. Demuth, Deep Learning Toolbox User’s Guide. Natick: The MathWorks, 2018.
M. Hagan and M. Menhaj, “Training feedforward networks with the marquardt algorithm,” IEEE Transactions on Neural Networks, vol. 5, no. 6, pp. 989–993, 1994. doi: 10.1109/72.329697 .
I. A. Basheer and M. Hajmeer, “Artificial neural networks: fundamentals, computing, design, and application,” Journal of microbiological methods, vol. 43, no. 1, pp. 3–31, 2000. doi: 10.1016/S0167-7012(00)00201-3 .
C. Bishop, Neural networks for pattern recognition. Clarendon Press, 1995, vol. 2.
R. Battiti, “First- and second-order methods for learning: Between steepest descent and newton’s method,” Neural Computation, vol. 4, no. 2, pp. 141–166, 1992. doi: 10.1162/neco.1992.4.2.141 .
R. Kohavi et al., “A study of cross-validation and bootstrap for accuracy estimation and model selection,” in Ijcai, vol. 14, no. 2. Montreal, Canada, 1995, pp. 1137–1145. doi: 10.5555/1643031.1643047 .
G. James, D. Witten, T. Hastie, and R. Tibshirani, An introduction to statistical learning with applications in R. Springer, 2013.
S. Russell and P. Norvig, Artificial Intelligence: A Modern Approach, 3rd ed. Upper Saddle River, NJ: Prentice Hall, 2010.