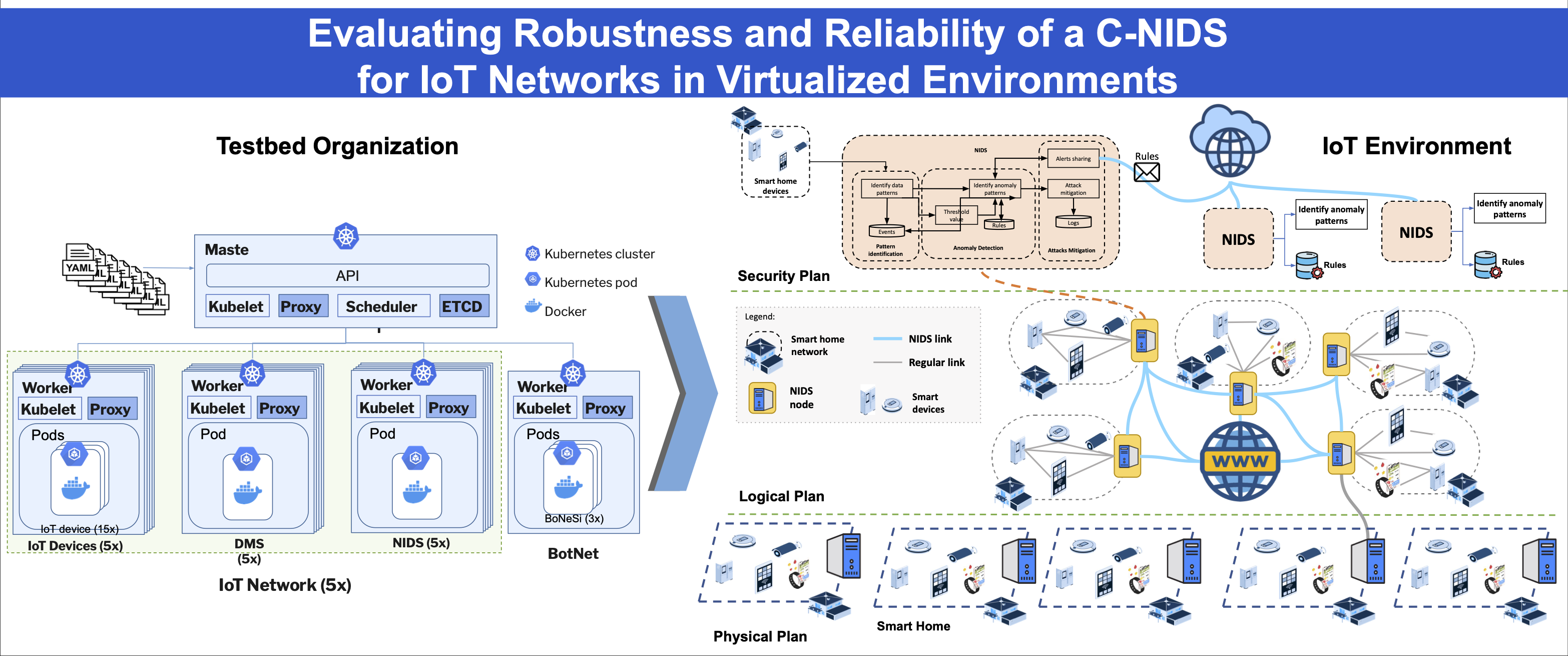
Evaluating Robustness and Reliability of a C-NIDS for IoT Networks in Virtualized Environments
Keywords:
Collaborative NIDS, Evaluation, Virtualization, Robustness, Reliability, IoTAbstract
Protecting thousands of smart devices across multiple IoT domains requires robust and collaborative security solutions, such as Collaborative Network Intrusion Detection Systems (C-NIDS). In this context, collaboration among NIDS improves intrusion detection by sharing information about local threats. However, most current solutions neglect the reliability and robustness assessment of these systems, especially when we consider C-NIDS. Thus, the lack of standardized and robust assessments to measure the reliability and accuracy of C-NIDS in attacks detection results in significant uncertainties regarding their ability to correctly identify threats. In this paper, we present an evaluation of a collaborative NIDS that integrates standalone NIDS to share information about detected and mitigated threats, improving overall intrusion detection. The evaluation took place in a virtualized IoT environment and results showed that collaborative NIDS detected DDoS attacks with an accuracy of at least 99.94%, a minimum recall of 99.94%, a precision of 100%, and F1 score of 1 in all evaluated scenarios. Such results highlight the development and adoption of uniform evaluation criteria to ensure the effectiveness and reliability of C-NIDS.
Downloads
References
B.Mbarek,M.Ge,andT.Pitner,“Enhancednetworkintrusiondetection system protocol for internet of things,” in Proceedings of the 35th annual ACM symposium on applied computing, pp. 1156–1163, ACM, 2020. doi: 10.1145/844128.844142.
S. Tanwar, N. Gupta, C. Iwendi, K. Kumar, and M. Alenezi, “Next Ge- neration IoT and Blockchain Integration,” Journal of Sensors, vol. 2022, 2022. doi: 10.1155/2022/9077348.
Y. R. Siwakoti, M. Bhurtel, D. B. Rawat, A. Oest, and R. Johnson, “Advances in IOT security: Vulnerabilities, enabled Criminal Services, attacks and countermeasures,” IEEE Internet of Things Journal, 2023. doi: 10.1109/JIOT.2023.3252594.
A. Heidari and M. A. Jabraeil Jamali, “Internet of Things intrusion de- tection systems: a comprehensive review and future directions,” Cluster Computing, vol. 26, no. 6, pp. 3753–3780, 2023. doi: 10.1007/s10586- 022-03776-z.
L. K. Vashishtha, A. P. Singh, and K. Chatterjee, “HIDM: A Hybrid Intrusion Detection Model for Cloud Based Systems,” Wireless Per- sonal Communications, vol. 128, no. 4, pp. 2637–2666, 2023. doi: 10.1007/s11277-022-10063-y.
L. Zhu, B. Zhao, W. Li, Y. Wang, and Y. An, “TICPS: A trustworthy collaborative intrusion detection framework for industrial cyber–physical systems,” Ad Hoc Networks, vol. 160, p. 103517, 2024. doi: 10.1016/j.adhoc.2024.103517.
K. Sood, D. D. N. Nguyen, M. R. Nosouhi, N. Kumar, F. Jiang, M. Chowdhury, and R. Doss, “Performance Evaluation of a Novel Intrusion Detection System in Next Generation Networks,” IEEE Tran- sactions on Network and Service Management, vol. 20, no. 3, pp. 3831– 3847, 2023. doi: 10.1109/TNSM.2023.3242270.
N. Moustafa, N. Koroniotis, M. Keshk, A. Y. Zomaya, and Z. Tari, “Explainable Intrusion Detection for Cyber Defences in the Internet of Things: Opportunities and Solutions,” IEEE Communications Surveys & Tutorials, 2023. doi: 10.1109/COMST.2023.3280465.
R. Sharma, C. A. Chan, and C. Leckie, “Evaluation of Centralised vs Distributed Collaborative Intrusion Detection Systems in Multi-Access Edge Computing,” in 2020 IFIP Networking Conference (Networking), pp. 343–351, IEEE, 2020. doi: 10.1007/978-3-030-69893-5_15.
V. Kumar, V. Kumar, N. Singh, and R. Kumar, “Enhancing Intrusion Detection System Performance to Detect Attacks on Edge of Things,” SN Computer Science, vol. 4, no. 6, p. 802, 2023. doi: 10.1007/s42979- 023-02242-w.
A. Ramos, M. Lazar, R. Holanda Filho, and J. J. Rodrigues, “A security metric for the evaluation of collaborative intrusion detection systems in wireless sensor networks,” in 2017 IEEE international conference on communications (ICC), pp. 1–6, IEEE, 2017. doi: 10.1109/ICC.2017.7997192.
J. Hesford, D. Cheng, A. Wan, L. Huynh, S. Kim, H. Kim, and J. B. Hong, “Expectations Versus Reality: Evaluating Intrusion Detection Systems in Practice,” arXiv preprint arXiv:2403.17458, 2024. doi: 10.48550/arXiv.2403.17458.
J. Gomez, E. F. Kfoury, J. Crichigno, and G. Srivastava, “A survey on network simulators, emulators, and testbeds used for research and education,” Computer Networks, vol. 237, p. 110054, 2023. doi: 10.1016/j.comnet.2023.110054.
C. Pedroso and A. Santos, “Dissemination control in dynamic data clus- tering for dense IIoT against false data injection attack,” International Journal of Network Management, p. e2201, 2022.
C.Pedroso,A.Batista,S.Brisio,G.Rodrigues,andA.Santos,“ADirect Collaborative Network Intrusion Detection System for IoT Networks Integration,” in Anais do XXXXII Simpósio Brasileiro de Redes de Computadores e Sistemas Distribuídos, pp. 477–490, SBC, 2024. doi: 10.5753/sbrc.2024.1354.
T. K. Authors, “KIND.” https://kind.sigs.k8s.io/, May 2023.
I. Tigera, “About Calico.” https://docs.tigera.io/calico/latest/about/, May
S. Madden, “Intel Lab Data.” https://db.csail.mit.edu/labdata/labdata.h
tml, June 2004.
Cisco, “What is Snort?.” https://www.snort.org/, May 2023.
M. Goldstein, “BoNeSi - The DDoS Botnet Simulator.” https://github.c
om/Markus-Go/bonesi, May 2023.
Netscout, “Global Attack Duration Breakdown (2H 2023) "https://www.netscout.com/threatreport/global-highlights/, Jan. 2024.
D.Powers,“Evaluation:FromPrecision,RecallandF-MeasuretoROC, Informedness, Markedness & Correlation,” Journal of Machine Learning Technologies, vol. 2, no. 1, pp. 37–63, 2011. doi: 10.9735/2229-3981.