FishEye Matlock: A Random Functional Encoding Mechanism for Secure Location Sharing
Keywords:
Location privacy, Access control, Location obfuscation, Matrix multiplication, Location-Based ServicesAbstract
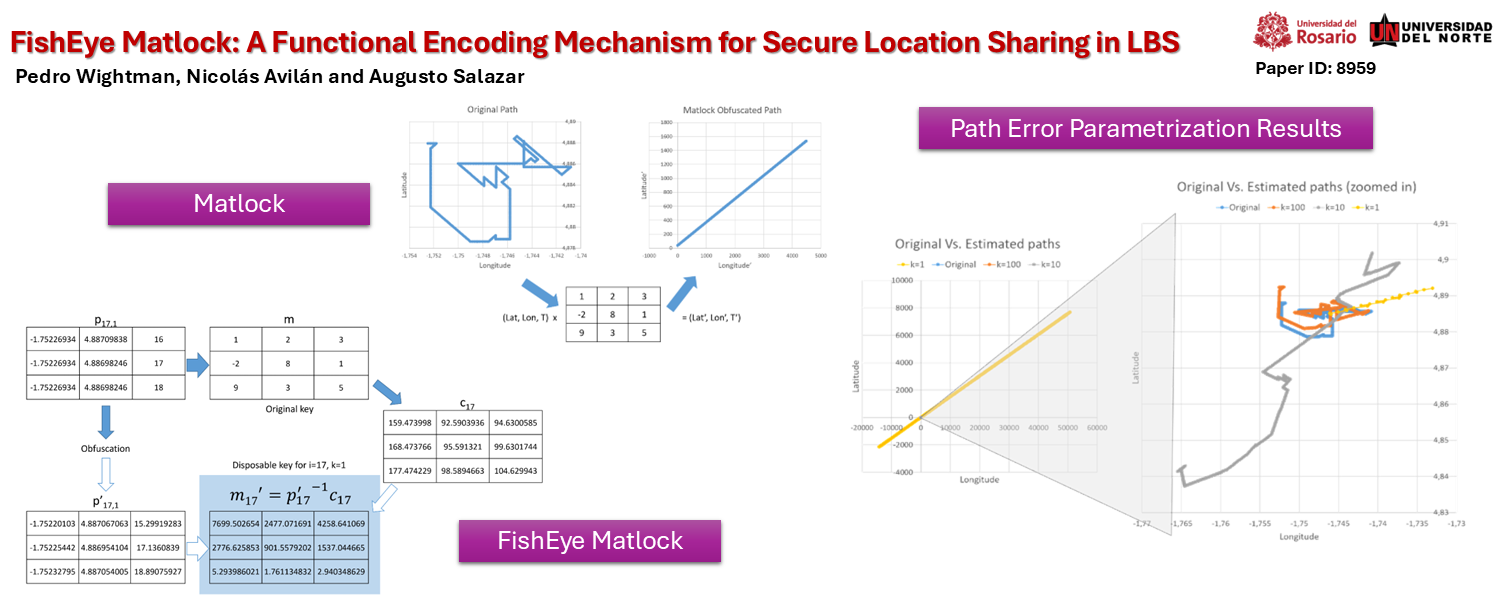
Location tracking is difficult to protect due to the sequential nature of the data and the need for accuracy to offer a proper service and monetize the location information. Homomorphic encryption can partially solve the problem, but it typically has a minimal set of operations that are not feasible for geographical operations. Randomized Functional Encoding (RFE) allows the creation of random keys to decrypt data, according to the user's needs. Now, creating keys that only focus on a portion of the path while protecting the rest of the path has not been proposed in the literature, to the knowledge of the authors. This work proposes a RFE mechanism for Matlock-coded location data, called FishEye Matlock. This technique generates disposable random key matrices that only reveal a desired portion of the path, with the possibility for the user to add random noise to protect the revealed data and to control the amount of noise added to the rest of the path. This allows secure information sharing with particular actors, like law enforcement, so that the information of interest is shared without affecting the user's privacy. The algorithm is tested in two different path scenarios to show the technique's applicability, the level of protection, and the impact of the parameter value selection. Results show that the mechanism can be tailored to generate key matrices for different scenarios: at the lowest value of k, the level of noise reaches several thousands of kilometers of noise along the path, and between 60 and 100 times the level of noise, and with, the highest k value, between 40% to 80% of the maximum distance radius on average at the point of interest, and between 1.1 and 10 times the defined noise level at the path.
Downloads
References
REFERENCES
M. Duckham and L. Kulik, “Location privacy and location-aware computing,” in Dynamic & mobile GIS: investigating change in space and time, R. Billen, E. Joao, and D. Forrest, Eds. CRC Press, 2006, ch. 3, pp. 35–51. [Online]. Available: https://doi.org/10.1201/9781420008609
S. Bai, G. Yang, J. Shi, G. Liu, and Z. Min, “Privacy-preserving oriented floating-point number fully homomorphic encryption scheme,” Security and Communication Networks, vol. 2018, no. 1, p. 2363928,
[Online]. Available: https://onlinelibrary.wiley.com/doi/abs/10.1155/2018/2363928
P. Wightman, M. Zurbarán, and A. Santander, “High variability geo-graphical obfuscation for location privacy,” in 2013 47th International Carnahan Conference on Security Technology (ICCST), 2013, pp. 1–6.
[Online]. Available: https://doi.org/10.1109/CCST.2013.6922079
C. Pang, C. Qiu, and N. Wang, “A geo-obfuscation approach to protect worker location privacy in spatial crowdsourcing systems,” in 2019 IEEE 16th International Conference on Mobile Ad Hoc and Sensor Systems Workshops (MASSW), 2019, pp. 166–167.
A. Dua, P. Singh, and J. Bapat, “Location privacy-preserving mechanism - a data-driven approach,” in 2021 IEEE International Conference on Electronics, Computing and Communication Technologies (CONECCT), 2021, pp. 1–6. [Online]. Available: https://doi.org/10.1109/CONECCT52877.2021.9622699
W. Cheng, R. Wen, H. Huang, W. Miao, and C. Wang, “Optdp: Towards optimal personalized trajectory differential privacy for trajectory data publishing,” Neurocomputing, vol. 472, pp. 201–211, 2022. [Online]. Available: https://doi.org/10.1016/j.neucom.2021.04.137
Y. Chen, A. Machanavajjhala, M. Hay, and G. Miklau, “Pegasus: Data-adaptive differentially private stream processing,” in Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, ser. CCS ’17. New York, NY, USA: Association for Computing Machinery, 2017, p. 1375–1388. [Online]. Available: https://doi.org/10.1145/3133956.3134102
I. Ullah, M. A. Shah, A. Wahid, A. Mehmood, and H. Song, “Esot: a new privacy model for preserving location privacy in internet of things,” Telecommunication Systems, vol. 67, no. 4, pp. 553–575, Apr 2018. [Online]. Available: https://doi.org/10.1007/s11235-017-0352-x
Z. Gao, Y. Huang, L. Zheng, H. Lu, B. Wu, and J. Zhang, “Protecting location privacy of users based on trajectory obfuscation in mobile crowdsensing,” IEEE Transactions on Industrial Informatics, vol. 18, no. 9, pp. 6290–6299, 2022. [Online]. Available: https: //doi.org/10.1109/TII.2022.3146281
M. Zurbaran and P. Wightman, “Voka: Voronoi k-aggregation mechanism for privacy in location-based information systems,” in 2017 International Carnahan Conference on Security Technology (ICCST), 2017, pp. 1–6. [Online]. Available: https://doi.org/10.1109/CCST.2017.8167857
P. M. Wightman, M. A. Jimeno, D. Jabba, and M. Labrador, “Matlock: A location obfuscation technique for accuracy-restricted applications,” in 2012 IEEE Wireless Communications and Networking
Conference (WCNC), 2012, pp. 1829–1834. [Online]. Available: https://doi.org/10.1109/WCNC.2012.6214082
V. A. Kachore, J. Lakshmi, and S. Nandy, “Location obfuscation for location data privacy,” in 2015 IEEE World Congress on Services, 2015, pp. 213–220. [Online]. Available: https://doi.org/10.1109/SERVICES.2015.39
X. Zhu, Y. Lu, X. Zhu, and S. Qiu, “A location privacy-preserving protocol based on homomorphic encryption and key agreement,” in 2013 International Conference on Information Science and
Cloud Computing Companion, 2013, pp. 54–59. [Online]. Available: https://doi.org/10.1109/ISCC-C.2013.17
S. Gupta and G. Arora, “Use of homomorphic encryption with gps in location privacy,” in 2019 4th International Conference on Information Systems and Computer Networks (ISCON), 2019, pp. 42–45. [Online]. Available: https://doi.org/10.1109/ISCON47742.2019.9036149
H. Shen, M. Zhang, H. Wang, F. Guo, and W. Susilo, “A lightweight privacy-preserving fair meeting location determination scheme,” IEEE Internet of Things Journal, vol. 7, no. 4, pp. 3083–3093, 2020. [Online]. Available: https://doi.org/10.1109/JIOT.2020.2965065
D. Boneh, A. Sahai, and B. Waters, “Functional encryption: Definitions and challenges,” in Theory of Cryptography, Y. Ishai, Ed. Berlin, Heidelberg: Springer Berlin Heidelberg, 2011, pp. 253–273. [Online].
Available: https://doi.org/10.1007/978-3-642-19571-6_16
J. Alwen, M. Barbosa, P. Farshim, R. Gennaro, S. D. Gordon, S. Tessaro, and D. A. Wilson, “On the relationship between functional encryption, obfuscation, and fully homomorphic encryption,” in Cryptography and Coding, M. Stam, Ed. Berlin, Heidelberg: Springer Berlin Heidelberg, 2013, pp. 65–84. [Online]. Available: https://doi.org/10.1007/978-3-642-45239-0_5
C. Yang, P. Jiang, and L. Zhu, “Accelerating decentralized and partial-privacy data access for vanet via online/offline functional encryption,” IEEE Transactions on Vehicular Technology, vol. 71, no. 8, pp. 8944–8954, 2022. [Online]. Available: https://doi.org/10.1109/TVT.2022.3174888
A. Kaminsky, M. Kurdziel, S. Farris, M. Łukowiak, and S. Radziszowski, “Solving the cross domain problem with functional encryption,” in MILCOM 2021 - 2021 IEEE Military Communications Conference (MILCOM), 2021, pp. 49–54. [Online]. Available: https://doi.org/10.1109/MILCOM52596.2021.9652958
D. Sharma and D. C. Jinwala, “Encrypted data ordering with functional encryption,” in 2018 4th International Conference on Recent Advances in Information Technology (RAIT), 2018, pp. 1–8. [Online]. Available: https://doi.org/10.1109/RAIT.2018.8389084
D. Li, J. Wu, J. Le, X. Liao, and T. Xiang, “A novel privacy-preserving location-based services search scheme in outsourced cloud,” IEEE Transactions on Cloud Computing, vol. 11, no. 1, pp. 457–469, 2023. [Online]. Available: https://doi.org/10.1109/TCC.2021.3098420
L. Gonzalez, M. Zurbarán, P. Wightman, D. Jabba, M. Jimeno, and E. Zurek, “Sensitivity analysis and countermeasures for transformation-based location obfuscation,” in 2014 International Carnahan Conference on Security Technology (ICCST), 2014, pp. 1–6. [Online]. Available: https://doi.org/10.1109/CCST.2014.6987048
P. Wightman, W. Coronell, D. Jabba, M. Jimeno, and M. Labrador, “Evaluation of location obfuscation techniques for privacy in location based information systems,” in 2011 IEEE Third Latin-American Conference on Communications, 2011, pp. 1–6. [Online]. Available: https://doi.org/10.1109/LatinCOM.2011.6107399