A Recommending Move Method Refactoring Opportunities Based on Feature Fusion and Deep Learning
Keywords:
Move Method, Refactoring, Feature Envy, Deep learning, Feature FusionAbstract
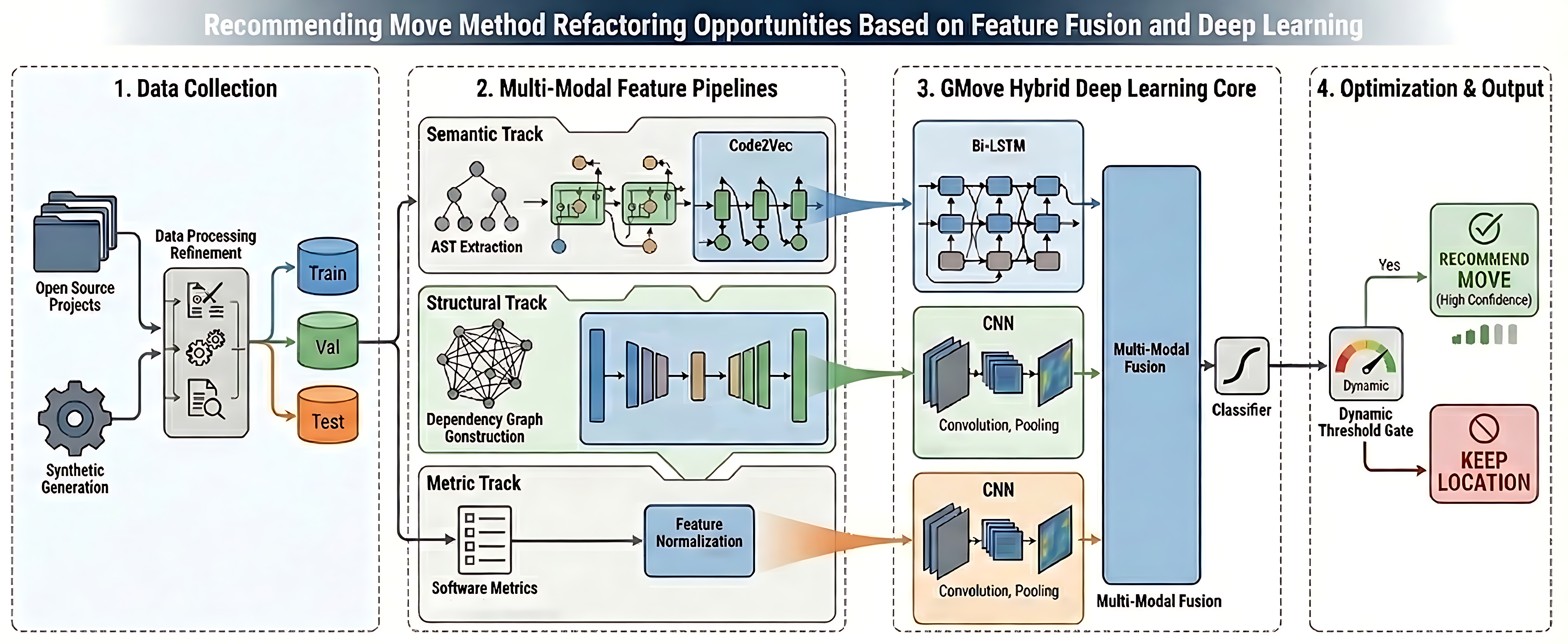
The Move Method refactoring is crucial for mitigating the Feature Envy code smell, which enhances cohesion and reduces coupling by relocating methods to more suitable classes. Existing deep learning approaches often suffer from redundant features, limiting model generalization. To address this, this paper introduces GMove, a novel approach leveraging feature fusion and a hybrid deep learning architecture (Bi-LSTM and CNN branches) to recommend refactoring opportunities. By fusing semantic, structural, and metric features from a constructed 16,828-sample dataset, GMove effectively filters redundant information. Experimental results demonstrate that GMove achieves a high synthetic F1 score of 97.7% and significantly outperforms state-of-the-art refactoring tools, showing an average F1 improvement of 9.7% over the strongest modern baseline, affirming its effectiveness and novel fusion strategy.
Downloads
References
M. Fowler, “Refactoring,” in Proceedings of the 24th
International Conference on Software Engineering, ser. ICSE
’02. New York, NY, USA: Association for Computing
Machinery, 2002, p. 701. [Online]. Available: https://doi.org/
1145/581339.581453
Y. Zhang, C. Ge, H. Liu, and K. Zheng, “Code smell
detection based on supervised learning models: A survey,”
Neurocomputing, vol. 565, p. 127014, 2024. [Online]. Available:
https://doi.org/10.1016/j.neucom.2023.127014
L. Chen and S. Hayashi, “Impact of change granularity in
refactoring detection,” in Proceedings of the 30th IEEE/ACM
International Conference on Program Comprehension, ser.
ICPC ’22. New York, NY, USA: Association for Computing
Machinery, 2022, p. 565–569. [Online]. Available: https:
//doi.org/10.1145/3524610.3528386
N. Tsantalis and A. Chatzigeorgiou, “Identification of move
method refactoring opportunities,” IEEE Transactions on
Software Engineering, vol. 35, no. 3, pp. 347–367, 2009.
[Online]. Available: https://doi.org/10.1109/TSE.2009.1
Y. Zhang, K. Guan, and L. Fang, “Mirror: multi-objective
refactoring recommendation via correlation analysis,” Automated
Software Engineering, vol. 31, no. 1, p. 2, 2024. [Online].
Available: https://doi.org/10.1007/s10515-023-00400-1
R. Terra, M. T. Valente, S. Miranda, and V. Sales, “Jmove:
A novel heuristic and tool to detect move method refactoring
opportunities,” Journal of Systems and Software, vol. 138, pp.
–36, 2018. [Online]. Available: https://doi.org/10.1016/j.jss.
11.073
M. Fokaefs, N. Tsantalis, and A. Chatzigeorgiou, “Jdeodorant:
Identification and removal of feature envy bad smells,” in
IEEE International Conference on Software Maintenance,
, pp. 519–520. [Online]. Available: https://doi.org/10.
/ICSM.2007.4362679
G. Bavota, R. Oliveto, M. Gethers, D. Poshyvanyk, and
A. De Lucia, “Methodbook: Recommending move method
refactorings via relational topic models,” IEEE Transactions
on Software Engineering, vol. 40, no. 7, pp. 671–694, 2014.
[Online]. Available: https://doi.org/10.1109/TSE.2013.60
Z. Kurbatova, I. Veselov, Y. Golubev, and T. Bryksin,
“Recommendation of move method refactoring using path-based
representation of code,” in Proceedings of the IEEE/ACM 42nd
International Conference on Software Engineering Workshops,
ser. ICSEW’20. New York, NY, USA: Association for
Computing Machinery, 2020, p. 315–322. [Online]. Available:
https://doi.org/10.1145/3387940.3392191
D. Cui, S. Wang, Y. Luo, X. Li, J. Dai, L. Wang, and
Q. Li, “Rmove: Recommending move method refactoring
opportunities using structural and semantic representations of
code,” in 2022 IEEE International Conference on Software
Maintenance and Evolution (ICSME), 2022, pp. 281–292.
[Online]. Available: https://doi.org/10.1109/ICSME55016.2022.
D. Cui, J. Wang, Q. Wang, P. Ji, M. Qiao, Y. Zhao,
J. Hu, L. Wang, and Q. Li, “Three heads are better
than one: Suggesting move method refactoring opportunities
with inter-class code entity dependency enhanced hybrid
hypergraph neural network,” in Proceedings of the 39th
IEEE/ACM International Conference on Automated Software
Engineering, ser. ASE ’24. New York, NY, USA: Association
for Computing Machinery, 2024, p. 745–757. [Online]. Available:
https://doi.org/10.1145/3691620.3695068
W. Ma, Y. Yu, X. Ruan, and B. Cai, “Pre-trained model
based feature envy detection,” in 2023 IEEE/ACM 20th
International Conference on Mining Software Repositories
(MSR), 2023, pp. 430–440. [Online]. Available: https://doi.org/
1109/MSR59073.2023.00065
B. Liu, H. Liu, G. Li, N. Niu, Z. Xu, Y. Wang, Y. Xia,
Y. Zhang, and Y. Jiang, “Deep learning based feature envy
detection boosted by real-world examples,” in Proceedings of
the 31st ACM Joint European Software Engineering Conference
and Symposium on the Foundations of Software Engineering,
ser. ESEC/FSE 2023. New York, NY, USA: Association for
Computing Machinery, 2023, p. 908–920. [Online]. Available:
https://doi.org/10.1145/3611643.3616353
Y. Wang, W. Wang, S. Joty, and S. C. H. Hoi, “Codet5:
Identifier-aware unified pre-trained encoder-decoder models for
code understanding and generation,” 2021. [Online]. Available:
https://arxiv.org/abs/2109.00859
E. Novozhilov, I. Veselov, M. Pravilov, and T. Bryksin,
“Evaluation of move method refactorings recommendation
algorithms: Are we doing it right?” in 2019 IEEE/ACM
rd International Workshop on Refactoring (IWoR), 2019,
pp. 23–26. [Online]. Available: https://doi.org/10.1109/IWoR.
00012
V. Kovalenko, E. Bogomolov, T. Bryksin, and A. Bacchelli,
“Pathminer: A library for mining of path-based representations
of code,” in 2019 IEEE/ACM 16th International Conference
on Mining Software Repositories (MSR), 2019, pp. 13–17.
[Online]. Available: https://doi.org/10.1109/MSR.2019.00013
U. Alon, M. Zilberstein, O. Levy, and E. Yahav, “Code2vec:
Learning distributed representations of code,” Proc. ACM
Program. Lang., vol. 3, no. POPL, jan 2019. [Online]. Available:
https://doi.org/10.1145/3290353
H. Cai and R. Santelices, “Abstracting program dependencies
using the method dependence graph,” in 2015 IEEE
International Conference on Software Quality, Reliability
and Security, 2015, pp. 49–58. [Online]. Available: https:
//doi.org/10.1109/QRS.2015.18
D. Wang, P. Cui, and W. Zhu, “Structural deep network
embedding,” in Proceedings of the 22nd ACM SIGKDD
International Conference on Knowledge Discovery and Data
Mining, ser. KDD ’16. New York, NY, USA: Association for
Computing Machinery, 2016, p. 1225–1234. [Online]. Available:
https://doi.org/10.1145/2939672.2939753
A. Z. Mustaqim, S. Adi, Y. Pristyanto, and Y. Astuti,
“The effect of recursive feature elimination with crossvalidation
(rfecv) feature selection algorithm toward classifier
performance on credit card fraud detection,” pp. 270–275, 2021.
[Online]. Available: https://doi.org/10.1109/ICAICST53116.
9497842
M. Schuster and K. Paliwal, “Bidirectional recurrent neural
networks,” IEEE Transactions on Signal Processing, vol. 45,
no. 11, pp. 2673–2681, 1997. [Online]. Available: https:
//doi.org/10.1109/78.650093
S. Skansi, “Convolutional neural networks,” pp. 121–
, 2018. [Online]. Available: https://doi.org/10.1007/
-3-319-73004-2_6
S. Safavian and D. Landgrebe, “A survey of decision tree
classifier methodology,” IEEE Transactions on Systems, Man,
and Cybernetics, vol. 21, no. 3, pp. 660–674, 1991. [Online].
Available: https://doi.org/10.1109/21.97458
W. S. Noble, “What is a support vector machine?” Nature
biotechnology, vol. 24, no. 12, pp. 1565–1567, 2006. [Online].
Available: https://doi.org/10.1038/nbt1206-1565
H. C. Jessen, “Applied logistic regression analysis,” Journal
of the Royal Statistical Society Series D: The Statistician,
vol. 45, no. 4, pp. 534–535, 12 2018. [Online]. Available:
https://doi.org/10.2307/2988559
M. Pal, “Random forest classifier for remote sensing
classification.” vol. 26, p. 217–222, 2005. [Online]. Available:
https://doi.org/10.1080/01431160412331269698
J. Simm and I. Abril, “Extratrees: extremely randomized
trees (extratrees) method for classification and regression,”
R package version, vol. 1, no. 5, 2014. [Online]. Available:
https://doi.org/10.1007/s10994-006-6226-1
S.-B. Kim, K.-S. Han, H.-C. Rim, and S. H. Myaeng,
“Some effective techniques for naive bayes text classification,”
vol. 18, no. 11, 2006, pp. 1457–1466. [Online]. Available:
https://doi.org/10.1109/TKDE.2006.180
R. Terra, L. F. Miranda, M. T. Valente, and R. S.
Bigonha, “Qualitas.class corpus: a compiled version of the
qualitas corpus,” SIGSOFT Softw. Eng. Notes, vol. 38,
no. 5, p. 1–4, Aug. 2013. [Online]. Available: https:
//doi.org/10.1145/2507288.2507314